Articles By This Author
New RFP Template for AI Usage Control and AI Governance
As AI becomes the central engine for enterprise productivity, security leaders are finally getting the green light — and the budget — to secure it. But there’s a quiet crisis unfolding in the boardroom: many organizations know they need “AI Governance,” but they have no idea what they are actually looking for. The CISO’s Dilemma: […]
Fake Laravel Packages on Packagist Deploy RAT on Windows, macOS, and Linux
Cybersecurity researchers have flagged malicious Packagist PHP packages masquerading as Laravel utilities that act as a conduit for a cross-platform remote access trojan (RAT) that’s functional on Windows, macOS, and Linux systems. The names of the packages are listed below – nhattuanbl/lara-helper (37 Downloads) nhattuanbl/simple-queue (29 Downloads) nhattuanbl/lara-swagger (49 Downloads)
APT41-Linked Silver Dragon Targets Governments Using Cobalt Strike and Google Drive C2
Cybersecurity researchers have disclosed details of an advanced persistent threat (APT) group dubbed Silver Dragon that has been linked to cyber attacks targeting entities in Europe and Southeast Asia since at least mid-2024. “Silver Dragon gains its initial access by exploiting public-facing internet servers and by delivering phishing emails that contain malicious attachments,” Check Point […]
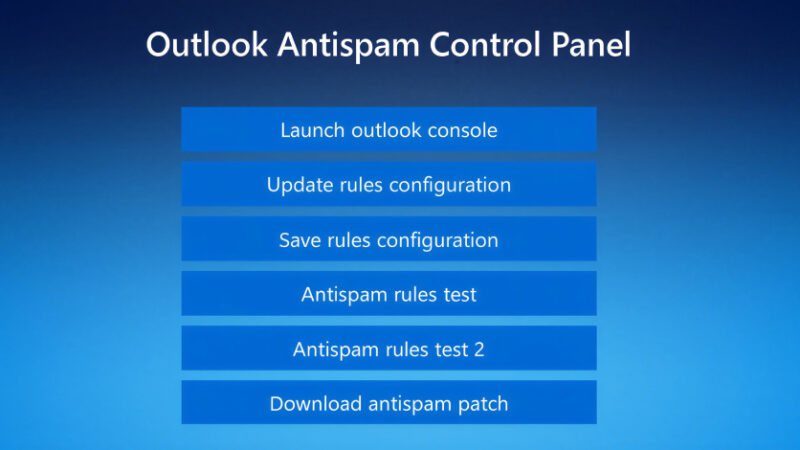
Fake Tech Support Spam Deploys Customized Havoc C2 Across Organizations
Threat hunters have called attention to a new campaign as part of which bad actors masqueraded as fake IT support to deliver the Havoc command-and-control (C2) framework as a precursor to data exfiltration or ransomware attack. The intrusions, identified by Huntress last month across five partner organizations, involved the threat actors using email spam as […]
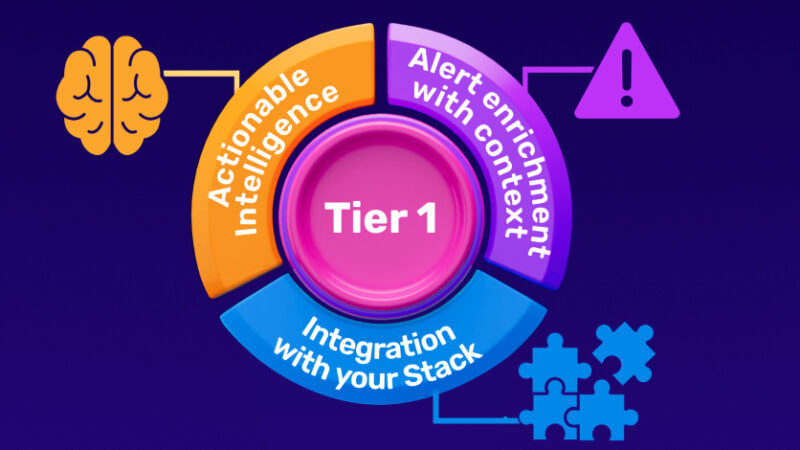
Building a High-Impact Tier 1: The 3 Steps CISOs Must Follow
Every CISO knows the uncomfortable truth about their Security Operations Center: the people most responsible for catching threats in real time are the people with the least experience. Tier 1 analysts sit at the front line of detection, and yet they are also the most vulnerable to the cognitive and organizational pressures that quietly erode […]
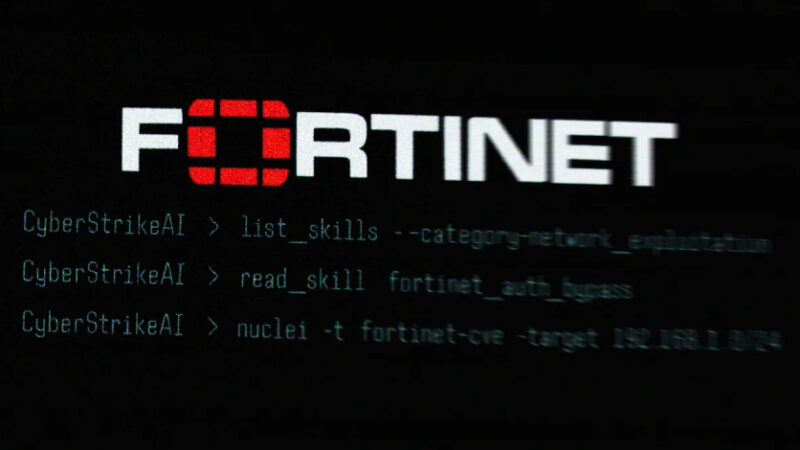
Open-Source CyberStrikeAI Deployed in AI-Driven FortiGate Attacks Across 55 Countries
The threat actor behind the recently disclosed artificial intelligence (AI)-assisted campaign targeting Fortinet FortiGate appliances leveraged an open-source, AI-native security testing platform called CyberStrikeAI to execute the attacks. The new findings come from Team Cymru, which detected its use following an analysis of the IP address (“212.11.64[.]250”) that was used by the suspected
AI Agents: The Next Wave Identity Dark Matter – Powerful, Invisible, and Unmanaged
The Rise of MCPs in the Enterprise The Model Context Protocol (MCP) is quickly becoming a practical way to push LLMs from “chat” into real work. By providing structured access to applications, APIs, and data, MCP enables prompt-driven AI agents that can retrieve information, take action, and automate end-to-end business workflows across the enterprise. This […]
Starkiller Phishing Suite Uses AitM Reverse Proxy to Bypass Multi-Factor Authentication
Cybersecurity researchers have disclosed details of a new phishing suite called Starkiller that proxies legitimate login pages to bypass multi-factor authentication (MFA) protections. It’s advertised as a cybercrime platform by a threat group calling itself Jinkusu, granting customers access to a dashboard that lets them select a brand to impersonate or enter a brand’s real […]
New Chrome Vulnerability Let Malicious Extensions Escalate Privileges via Gemini Panel
Cybersecurity researchers have disclosed details of a now-patched security flaw in Google Chrome that could have permitted attackers to escalate privileges and gain access to local files on the system. The vulnerability, tracked as CVE-2026-0628 (CVSS score: 8.8), has been described as a case of insufficient policy enforcement in the WebView tag. It was patched […]
Google Develops Merkle Tree Certificates to Enable Quantum-Resistant HTTPS in Chrome
Google has announced a new program in its Chrome browser to ensure that HTTPS certificates are secure against the future risk posed by quantum computers. “To ensure the scalability and efficiency of the ecosystem, Chrome has no immediate plan to add traditional X.509 certificates containing post-quantum cryptography to the Chrome Root Store,” the Chrome Secure […]