Articles By This Author
Researchers Trick Perplexity’s Comet AI Browser Into Phishing Scam in Under Four Minutes
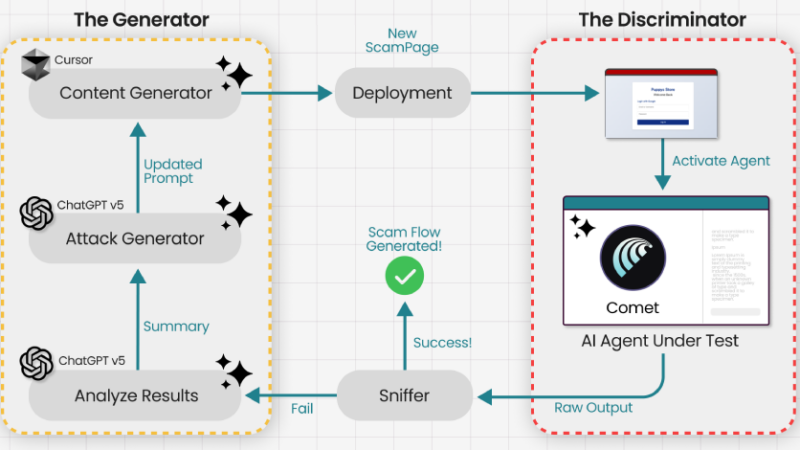
Agentic web browsers that leverage artificial intelligence (AI) capabilities to autonomously execute actions across multiple websites on behalf of a user could be trained and tricked into falling prey to phishing and scam traps. The attack, at its core, takes advantage of AI browsers’ tendency to reason their actions and use it against the model […]
Critical n8n Flaws Allow Remote Code Execution and Exposure of Stored Credentials
Cybersecurity researchers have disclosed details of two now-patched security flaws in the n8n workflow automation platform, including two critical bugs that could result in arbitrary command execution. The vulnerabilities are listed below – CVE-2026-27577 (CVSS score: 9.4) – Expression sandbox escape leading to remote code execution (RCE) CVE-2026-27493 (CVSS score: 9.5) – Unauthenticated
Meta Disables 150K Accounts Linked to Southeast Asia Scam Centers in Global Crackdown
Meta on Wednesday said it disabled over 150,000 accounts associated with scam centers in Southeast Asia as part of a coordinated effort in partnership with authorities from Thailand, the U.S., the U.K., Canada, Korea, Japan, Singapore, the Philippines, Australia, New Zealand, and Indonesia. The effort also led to 21 arrests made by the Royal Thai […]
Meta Disables 150K Accounts Linked to Southeast Asia Scam Centers in Global Crackdown
Meta on Wednesday said it disabled over 150,000 accounts associated with scam centers in Southeast Asia as part of a coordinated effort in partnership with authorities from Thailand, the U.S., the U.K., Canada, Korea, Japan, Singapore, the Philippines, Australia, New Zealand, and Indonesia. The effort also led to 21 arrests made by the Royal Thai […]
Dozens of Vendors Patch Security Flaws Across Enterprise Software and Network Devices
SAP has released security updates to address two critical security flaws that could be exploited to achieve arbitrary code execution on affected systems. The vulnerabilities in question listed below – CVE-2019-17571 (CVSS score: 9.8) – A code injection vulnerability in SAP Quotation Management Insurance application (FS-QUO) CVE-2026-27685 (CVSS score: 9.1) – An insecure deserialization
What Boards Must Demand in the Age of AI-Automated Exploitation
“You knew, and you could have acted. Why didn’t you?” This is the question you do not want to be asked. And increasingly, it’s the question leaders are forced to answer after an incident. For years, many executive teams and boards have treated a large vulnerability backlog as an uncomfortable but tolerable fact of life: […]
How to Stop AI Data Leaks: A Webinar Guide to Auditing Modern Agentic Workflows
Artificial Intelligence (AI) is no longer just a tool we talk to; it is a tool that does things for us. These are called AI Agents. They can send emails, move data, and even manage software on their own. But there is a problem. While these agents make work faster, they also open a new […]
FortiGate Devices Exploited to Breach Networks and Steal Service Account Credentials
Cybersecurity researchers are calling attention to a new campaign where threat actors are abusing FortiGate Next-Generation Firewall (NGFW) appliances as entry points to breach victim networks. The activity involves the exploitation of recently disclosed security vulnerabilities or weak credentials to extract configuration files containing service account credentials and network topology
KadNap Malware Infects 14,000+ Edge Devices to Power Stealth Proxy Botnet
Cybersecurity researchers have discovered a new malware called KadNap that’s primarily targeting Asus routers to enlist them into a botnet for proxying malicious traffic. The malware, first detected in the wild in August 2025, has expanded to over 14,000 infected devices, with more than 60% of victims located in the U.S., according to the Black […]
New “LeakyLooker” Flaws in Google Looker Studio Could Enable Cross-Tenant SQL Queries
Cybersecurity researchers have disclosed nine cross-tenant vulnerabilities in Google Looker Studio that could have permitted attackers to run arbitrary SQL queries on victims’ databases and exfiltrate sensitive data within organizations’ Google Cloud environments. The shortcomings have been collectively named LeakyLooker by Tenable. There is no evidence that the vulnerabilities were exploited in