TrueConf Zero-Day Exploited in Attacks on Southeast Asian Government Networks
A high-severity security flaw in the TrueConf client video conferencing software has been exploited in the wild as a zero-day as part of a campaign… Read MoreThe Hacker News
Vertex AI Vulnerability Exposes Google Cloud Data and Private Artifacts
Cybersecurity researchers have disclosed a security “blind spot” in Google Cloud’s Vertex AI platform that could allow artificial intelligence (AI) agents to be weaponized by… Read MoreThe Hacker News
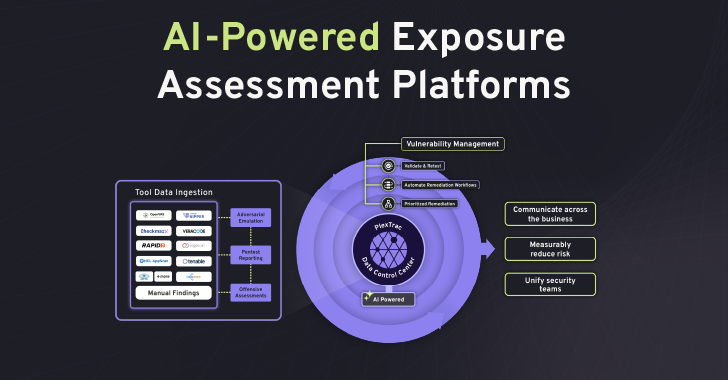
The AI Arms Race – Why Unified Exposure Management Is Becoming a Boardroom Priority
The cybersecurity landscape is accelerating at an unprecedented rate. What is emerging is not simply a rise in the number of vulnerabilities or tools, but… Read MoreThe Hacker News
Silver Fox Expands Asia Cyber Campaign with AtlasCross RAT and Fake Domains
Chinese-speaking users are the target of an active campaign that uses typosquatted domains impersonating trusted software brands to deliver a previously undocumented remote access trojan… Read MoreThe Hacker News
Axios Supply Chain Attack Pushes Cross-Platform RAT via Compromised npm Account
The popular HTTP client known as Axios has suffered a supply chain attack after two newly published versions of the npm package introduced a malicious… Read MoreThe Hacker News
⚡ Weekly Recap: Telecom Sleeper Cells, LLM Jailbreaks, Apple Forces U.K. Age Checks and More
Some weeks are loud. This one was quieter but not in a good way. Long-running operations are finally hitting courtrooms, old attack methods are showing… Read MoreThe Hacker News
3 SOC Process Fixes That Unlock Tier 1 Productivity
What is really slowing Tier 1 down: the threat itself or the process around it? In many SOCs, the biggest delays do not come from… Read MoreThe Hacker News
Russian CTRL Toolkit Delivered via Malicious LNK Files Hijacks RDP via FRP Tunnels
Cybersecurity researchers have discovered a remote access toolkit of Russian-origin that’s distributed via malicious Windows shortcut (LNK) files that are disguised as private key folders.… Read MoreThe Hacker News
The State of Secrets Sprawl 2026: 9 Takeaways for CISOs
Secrets sprawl isn’t slowing down: in 2025, it accelerated faster than most security teams anticipated. GitGuardian’s State of Secrets Sprawl 2026 report analyzed billions of… Read MoreThe Hacker News
Three China-Linked Clusters Target Southeast Asian Government in 2025 Cyber Campaign
Three threat activity clusters aligned with China have targeted a government organization in Southeast Asia as part of what has been described as a “complex… Read MoreThe Hacker News