Filling the Most Common Gaps in Google Workspace Security
Security teams at agile, fast-growing companies often have the same mandate: secure the business without slowing it down. Most teams inherit a tech stack optimized for breakneck growth, not resilience. In these environments, the security team is the helpdesk, the compliance expert, and the incident response team all rolled into one. Securing the cloud office […]
Malicious PyPI Package Impersonates SymPy, Deploys XMRig Miner on Linux Hosts
A new malicious package discovered in the Python Package Index (PyPI) has been found to impersonate a popular library for symbolic mathematics to deploy malicious payloads, including a cryptocurrency miner, on Linux hosts. The package, named sympy-dev, mimics SymPy, replicating the latter’s project description verbatim in an attempt to deceive unsuspecting users into thinking that […]
North Korean PurpleBravo Campaign Targeted 3,136 IP Addresses via Fake Job Interviews
As many as 3,136 individual IP addresses linked to likely targets of the Contagious Interview activity have been identified, with the campaign claiming 20 potential victim organizations spanning artificial intelligence (AI), cryptocurrency, financial services, IT services, marketing, and software development sectors in Europe, South Asia, the Middle East, and Central America. The new findings
Zoom and GitLab Release Security Updates Fixing RCE, DoS, and 2FA Bypass Flaws
Zoom and GitLab have released security updates to resolve a number of security vulnerabilities that could result in denial-of-service (DoS) and remote code execution. The most severe of the lot is a critical security flaw impacting Zoom Node Multimedia Routers (MMRs) that could permit a meeting participant to conduct remote code execution attacks. The vulnerability, […]
Webinar: How Smart MSSPs Using AI to Boost Margins with Half the Staff
Every managed security provider is chasing the same problem in 2026 — too many alerts, too few analysts, and clients demanding “CISO-level protection” at SMB budgets. The truth? Most MSSPs are running harder, not smarter. And it’s breaking their margins. That’s where the quiet revolution is happening: AI isn’t just writing reports or surfacing risks […]
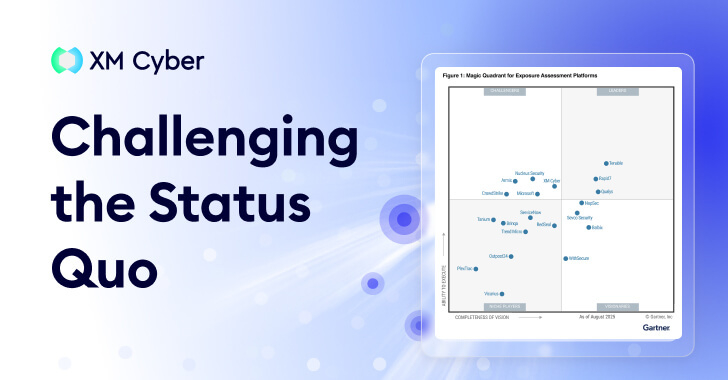
Exposure Assessment Platforms Signal a Shift in Focus
Gartner® doesn’t create new categories lightly. Generally speaking, a new acronym only emerges when the industry’s collective “to-do list” has become mathematically impossible to complete. And so it seems that the introduction of the Exposure Assessment Platforms (EAP) category is a formal admission that traditional Vulnerability Management (VM) is no longer a viable way to […]
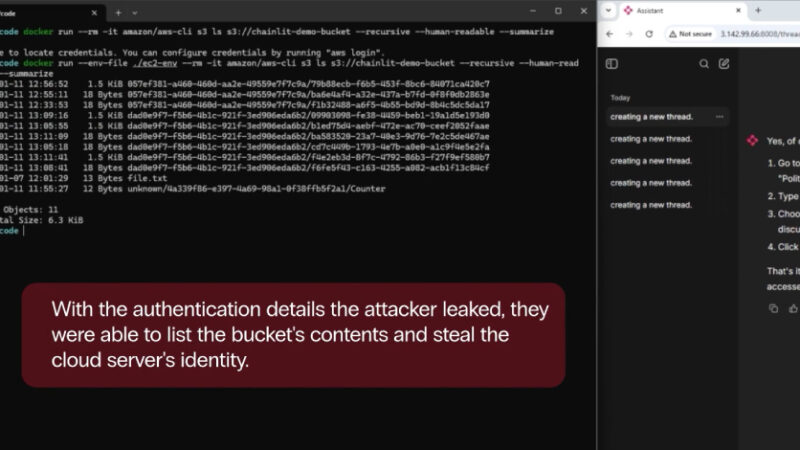
Chainlit AI Framework Flaws Enable Data Theft via File Read and SSRF Bugs
Security vulnerabilities were uncovered in the popular open-source artificial intelligence (AI) framework Chainlit that could allow attackers to steal sensitive data, which may allow for lateral movement within a susceptible organization. Zafran Security said the high-severity flaws, collectively dubbed ChainLeak, could be abused to leak cloud environment API keys and steal sensitive files, or
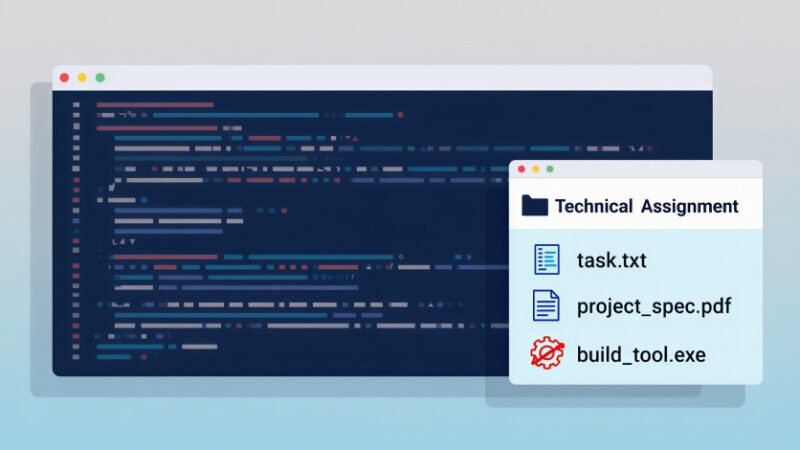
North Korea-Linked Hackers Target Developers via Malicious VS Code Projects
The North Korean threat actors associated with the long-running Contagious Interview campaign have been observed using malicious Microsoft Visual Studio Code (VS Code) projects as lures to deliver a backdoor on compromised endpoints. The latest finding demonstrates continued evolution of the new tactic that was first discovered in December 2025, Jamf Threat Labs said. “This […]
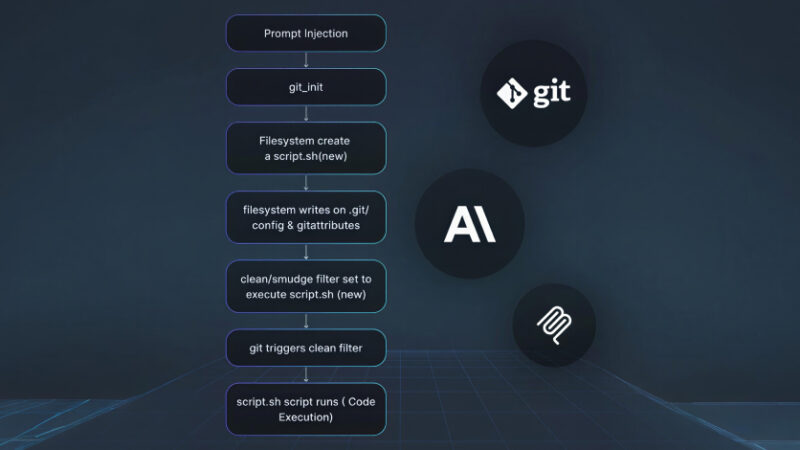
Three Flaws in Anthropic MCP Git Server Enable File Access and Code Execution
A set of three security vulnerabilities has been disclosed in mcp-server-git, the official Git Model Context Protocol (MCP) server maintained by Anthropic, that could be exploited to read or delete arbitrary files and execute code under certain conditions. “These flaws can be exploited through prompt injection, meaning an attacker who can influence what an AI […]
Hackers Use LinkedIn Messages to Spread RAT Malware Through DLL Sideloading
Cybersecurity researchers have uncovered a new phishing campaign that exploits social media private messages to propagate malicious payloads, likely with the intent to deploy a remote access trojan (RAT). The activity delivers “weaponized files via Dynamic Link Library (DLL) sideloading, combined with a legitimate, open-source Python pen-testing script,” ReliaQuest said in a report shared with